Closer Than Close
In both the pre-digital age and the digital age, when you examine the lives of bank robbers who…
Threat Hunting with Yara
Throughout the world, the trend of encrypting data on end-user systems with malicious software (such as Cryptolocker) and…
Threat Hunting
Sometimes, after writing a blog post about a malware, I find myself asking, “How would I detect this…
Hacker Hunt with a Deception System
I have been hearing this question more and more frequently from many people around me, both those I…
The APT Attempt
With each passing year, serious cyber security breaches are being experienced and institutions that learn from others’ experiences…
It’s a Bird… It’s a Plane… It’s Drone!
Unmanned Aerial Vehicles (UAVs), commonly known as drones, which can be easily purchased online with just a click…
Java Decompilers
I agree that working at byte code level is sometimes a bit challenging. If the mission is analyzing…
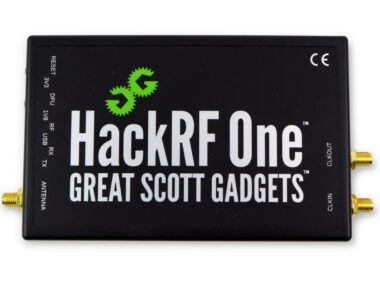
RF World and Security
Since I was a child, remote-controlled garage doors have always caught my attention. As I grew older and…